Keypress Management
Key management for efficient control of key handovers
Secure storage and electronic management of keys
Manual key management costs a lot of time and energy. A key is quickly lost, the trouble is enormous, searching for it is time-consuming and often unsuccessful. With more and more mechanical keys in circulation, you can quickly loose track. A manual issue of keys, e.g. for security-relevant buildings, rooms, commercial properties, industrial sites, vehicle parks and fleets, can result in an immense administrative effort, significant security gaps and very high costs.
Would you like to save yourself this hassle and your valuable time by leaving the key chaos behind? Would you like to have a better overview and full control over your numerous keys? Keypress Management provides efficient solutions for key management. With electronic key management, user access to individual keys can be pre-defined and clearly managed via the Commander Connect software.
- 100% maintenance free – thanks to RFID technology the keyTags attached to the keys operate contactless – this means inserting the tags in the slots does not result in any wear and tear.
- Local or global – Our software is web-based so it supports administration across multiple locations. This means you are easily able to centrally monitor systems in different locations.
- Software – A variety of features and modules for diverse applications. All access is automatically documented and the information issued in user definable reports.
- Emergency operation mode – All cabinets remain operational – even in the case of a power or network failure. The data is stored locally and an integrated emergency battery secures continued operation.
- Guaranteed future proof – All installed modules are replaceable and backwards compatible. If the requirements change, the system can move with the times accordingly.
- Made in Germany – Their function and quality are developed, produced and tested to the highest standards.
100% maintenance free
Thanks to RFID technology the keyTags attached to the keys operate contactless – this means inserting the tags in the slots does not result in any wear and tear.
Local or global
Our software is web-based so it supports administration across multiple locations. This means you are easily able to centrally monitor systems in different locations.
Software
A variety of features and modules for diverse applications. All access is automatically documented and the information issued in user definable reports.
Emergency operation mode
All cabinets remain operational - even in the case of a power or network failure. The data is stored locally and an integrated emergency battery secures continued operation.
Guaranteed future proof
All installed modules are replaceable and backwards compatible. If the requirements change, the system can move with the times accordingly.
Made in Germany
All products are made in Germany. Their function and quality are developed, produced and tested to the highest standards.
keyTag
Smart reliable identification for your keys
The keyTag is the heart of a key management system. Each keyTag has a unique identity so that its location within the cabinet is known.
The most important and critical part of the system must perform all of the time to ensure that you have access to the keys when you need them, that’s why proxSafe uses the most advanced identification technology available - RFID.
- Includes integral keyring and seal
- Contactless, so no wear
- Works without a battery


Terminal
User identification and control tasks
To gain access to the cabinet and keys there is a choice of control terminals that all include an integrated smartcard reader which allows most customers to make use of their existing proximity access control cards, PIN or both. There is also an option for biometric verification and a touch screen. The control terminal allows for full flexibility giving the option of having multiple key cabinets controlled from a single point or multiple control terminals controlling the same set of cabinets, this is an important consideration where disability discrimination regulations need to be met.
maxx
Compact and elegant key box with automatic door
The compact and elegant design of the maxx cabinet blends functionality of a professional key management system with a sleek design for use in a prominent location. The maxx cabinet allows full control over your keys whilst giving quick and easy access to keys when needed. The convenient and ultra reliable automatic roller shutter door keeps keys hidden from view and allows the cabinet to be located in areas such as a corridor where a conventional hinged door would be problematic due to space. Available in 32 or 64 keyTag capacity Maxx cabinets can be combined with other maxx or flexx cabinets where additional storage space is required and multiple cabinets can all be managed by the same control terminal.

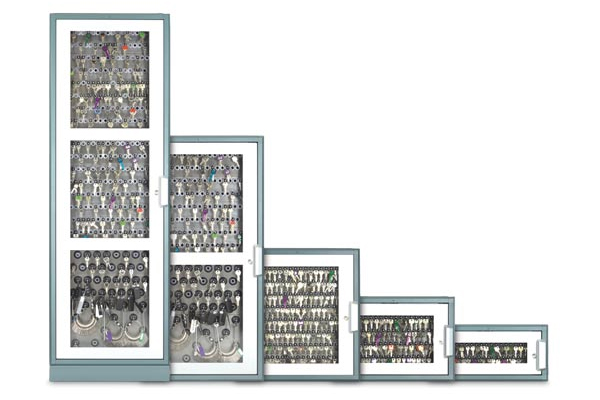
flexx
A scalable modular system
Flexx cabinets are available in a matching range of different sizes with a choice of either a solid steel or window door. The modular design allows a system to be easily adapted specifically for your current needs whilst leaving options open for future needs. Select a cabinet size, select keyTag panels and finally select a control terminal to meet your exact requirements. A variety of different internal keyTag panels allows each cabinet to be optimised to suit the different sizes and bunches of keys that are to be controlled. A system can be configured for maximum capacity by only using the wider spacing keyTag panels for those large bunches of keys that need more space. The keyTag panels can also be changed as needs change.
Equally the flexx cabinets allow you to invest in a system for today that leaves your options open for future expansion. Multiple cabinets can be connected together and managed by the same control terminal of your choice. You can add additional cabinets or keyTag panels at any time.
You may also like…
Guard Tour Management
Security guard and plant protection
Comprehensive recording of mobile and stationary security services
dataLog is the market leading proof-of-visit and patrol verification system, that records the presence and location of security, cleaning and maintenance personnel at given locations and times. dataLog systems allow better use of staff, improves efficiency, and provide accurate and fast audit information on work carried out. Most importantly they highlight any checks that were missed, so that appropriate action can be taken.
The main components to a dataLog proof-of-visit system are a handheld data collector, location checkpoints and management software. Checkpoints are fixed to locations to be visited, and the worker carries a robust handheld data collector which they use to read the checkpoint when it is visited. The checkpoints identification number and time of the visit is recorded by the data collector.
dataLog systems are ideal to determine the location of security guards and other workers where security, safety, servicing or cleaning checks need to be done. deister dataLog systems are used globally for manned guarding operations and many other applications where a mobile worker’s attendance at a given location needs to be verified.
- 100% maintenance free – Checkpoints are maintenance free, they do not contain batteries or hard wiring. The RFID proximity checkpoints are suitable for use internally or externally in all weather conditions.
- Easy to use – Checkpoints are easy to read, simply hold the data collector close to the checkpoint, that’s it. No buttons to press or apps to open.
- Long battery life – Best in class operational time with the guardiX II being able to read up to 500,000 checkpoints from a pair of AA batteries. With no recharging necessary the collector is always ready to use.
- Connected systems – dataLog works with other deister systems to allow events to be combined within common reports across different systems.
- Robust & reliable – The guardiX II is IP67 classified and has no buttons, switches or other external moving parts that could be prone to failure.
- Backwards compatible – guardiX II data collectors are backwards compatible with all deister RFID Checkpoints that have been supplied for many years.
Smart Storage System
Intelligent asset management systems with handling automation
Automatic issue and return of valuables
Are your important assets and resources used efficiently? It‘s often all to easy too lose track of who has what item, when it is last used and especially the condition that it is returned in. proxSafe smart storage systems identify who has your essential assets by controlling who has them with full audit and reporting capabilities. Users are identified by card, pin or biometrics allowing them to only take the items that they are authorised to have, ensuring you have complete accountability of your company’s shared portable equipment. Radios, test equipment, tools, laptops and much more can now be managed automatically so you know that the equipment is ready when you need it.
- Intelligent management - Intelligent resource monitoring controls removal of resources evenly with the same usage. Criteria parameters for the intelligent management of the items can be chosen.
- Local or global - Our software is web-based so it supports administration across multiple locations. This means you are easily able to centrally monitor systems in different locations.
- Software - A variety of features and modules for diverse applications. All access is automatically documented and the information issued in user definable reports.
- Emergency operation mode - All cabinets remain operational - even in the case of a power or network failure. The data is stored locally and an integrated emergency battery secures continued operation.
- Integrated charging - Ensure that the asset is ready for the next shift. Equipment can be charged whilst the item is stored in the cabinet. The state of charge is also displayed.
- Made in Germany - Their function and quality are developed, produced and tested to the highest standards.





