How Does Face Recognition Work? Is It Secure?
How Does Face Recognition Work? Is It Secure?
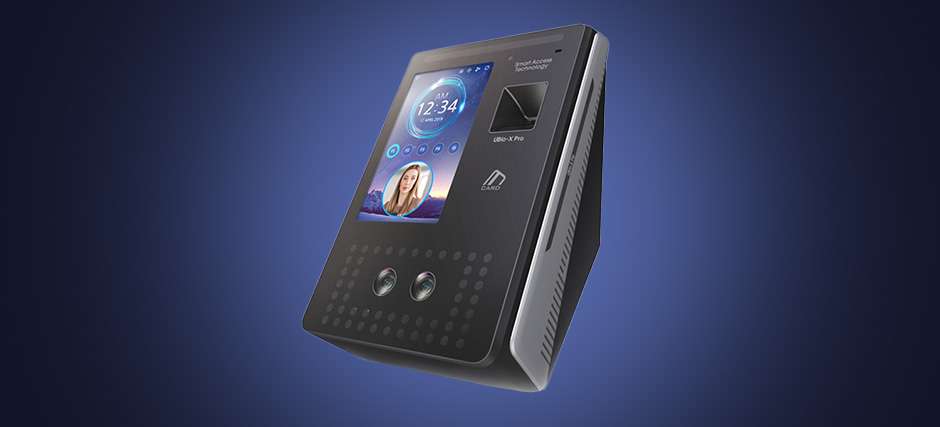
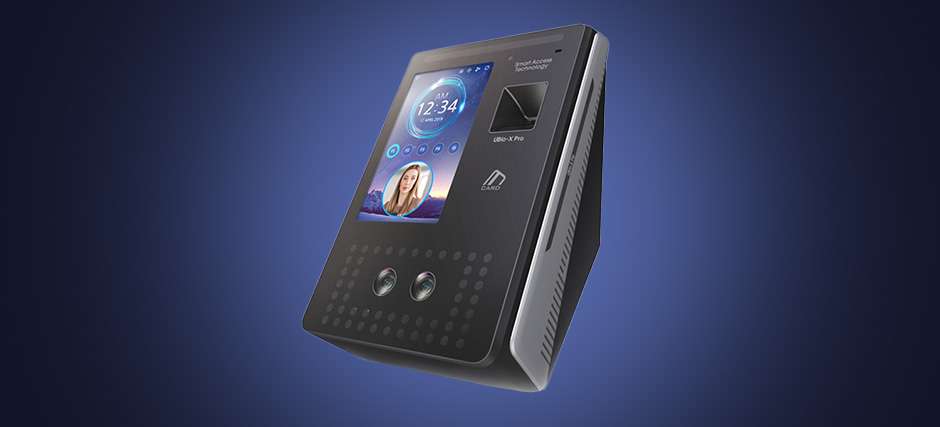
Whether it’s door access systems or personal gadgets, many authentication technologies have surfaced to enhance security, convenience, and privacy across various facets of our lives. Among them, the face recognition access control system stands out as a noteworthy example. It has seamlessly integrated into our daily routines, facilitating tasks such as unlocking smartphones and streamlining immigration procedures. But how exactly does this technology work? Is it truly secure? We discuss more below.
What is Face Recognition Technology?
Facial recognition is an advanced biometric technology that uses a person’s facial features to authenticate identities. The computers and software used are able to accurately grant or deny access by analysing the unique and distinctive characteristics of a person’s face and distinguishing them from others. For example, the distance between the eyes, nose shape, and contours of the cheeks.
This technology has received widespread attention and is widely used thanks to its amazing capabilities and potential to improve security and operational efficiency across various industries.
How Does Facial Recognition Work?
A face recognition system contains a combination of computer science, machine learning, and image processing technologies that work together to capture, analyse, and compare features to a database of known faces. This allows them to accurately identify and verify individuals based on their facial features. Here’s how it works:
1. Enrolment
An individual’s face is captured by a camera or device during set up. The captured facial image is then processed to extract relevant facial features and create a unique facial template, which is then stored in a database along with associated data such as the person’s name, ID, or other relevant information.
2. Face Detection

When someone is trying to gain access to a device or a facility, they will have to appear before the system, which will scan the area in order to locate facial landmarks like the eyes, nose, and mouth to determine the presence of a face. After face detection, the system will proceed to do feature extraction.
3. Feature Extraction
This is where specific facial features are captured and converted into numerical data. These can include distances between key facial landmarks, angles, and other distinctive attributes.
4. Face Representation
The extracted features are transformed into a mathematical representation, often referred to as a “faceprint” or facial template. It’ll consist of a set of data points that represent the unique characteristics of an individual’s face.
5. Database Comparison
The facial template is then compared to a database of stored templates, where information about known individuals, authorised users, or references faces are stored. The comparison involves calculating a similarity score or distance metric between the captured facial template and data stored.
6. Matching and Decision Making
The system makes a decision based on the similarity score. If the score exceeds a predetermined threshold, the system considers it a match, and the individual’s identity is confirmed. If there is no match, the person will be classified as an unknown individual and be denied access.
Is Facial Recognition Technology Safe and Secure?
Facial recognition relies on the complexity of an individual’s facial features to authenticate their identity. These features are unique to each person and are challenging to impersonate.
To prevent spoofing attempts using static images or videos, many face recognition access control systems incorporate liveness detection mechanisms to asses the liveliness of the presented face, requiring individuals to blink, nod, or perform other actions to prove they are real, live people to the biometric system.
Some face recognition door access systems are also combined with other authentication factors, such as a PIN or fingerprint, to add an additional layer of protection, reduce the risk of unauthorised access and enhance security.
Learn More: Why Your Business Will Benefit from Multi-Modal Biometric Systems
Other technologies and efforts such as encryption, data anonymisation, regular security patches and detailed audit trails help to maintain a robust system that can effectively safeguard against unauthorised access.
Looking for a face recognition access control system that can bolster the security of your premises? iDLink Systems is a leading provider of electronic security solutions in Singapore. Check out our product catalogue here.
